Billing Quota Management
Learn about what counts towards your quota and how to manage your quota.
Data and quotas are interconnected in Sentry. When you subscribe to Sentry, you pay for the amount of data - events (errors, replays, spans or transactions, and profiles), and attachments - to be tracked. Each data category has its own quota that you can adjust. When Sentry tracks an event or attachment, it counts toward your quota for that type of data.
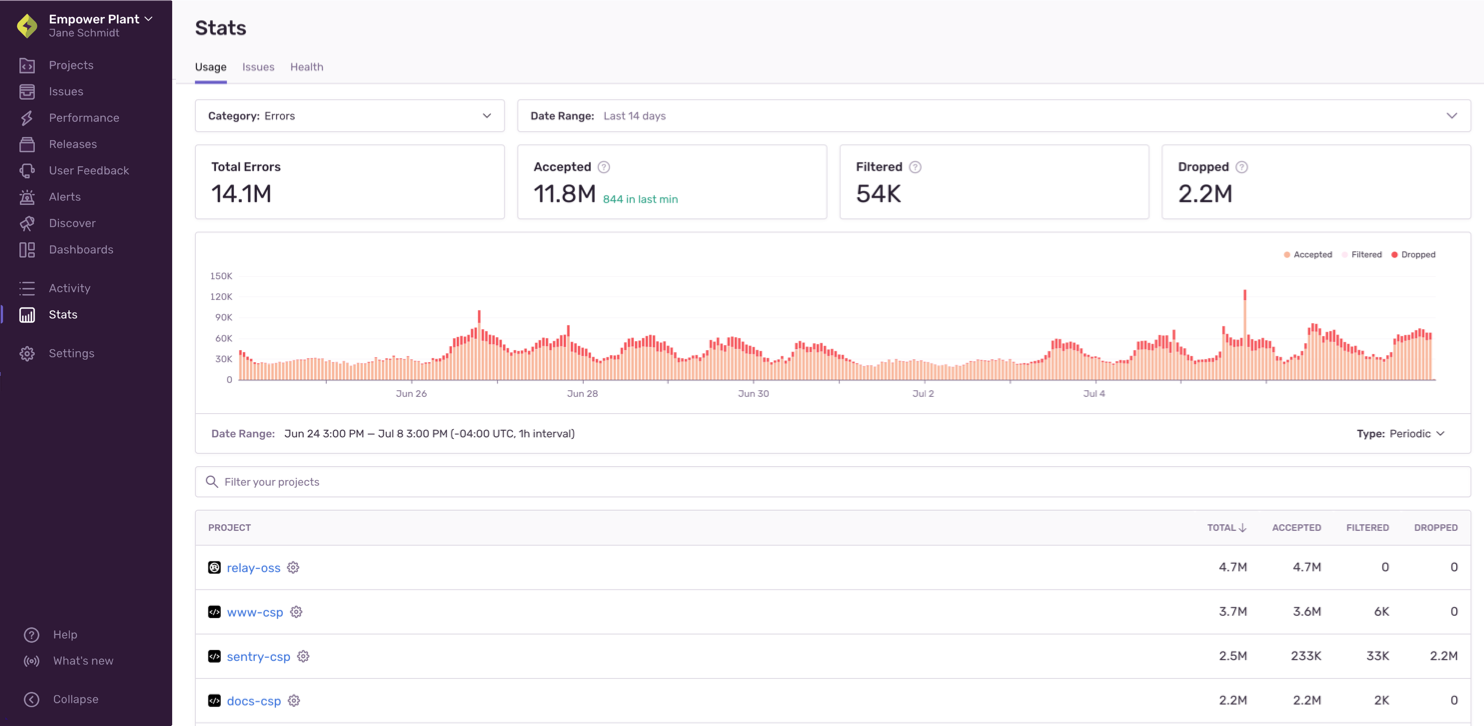
To see which projects are using up your quota, you can review the "Usage" tab of Stats. This page can be viewed by any member of your organization. In addition, you can come back to this page to check if the changes you've made are having the desired effect:
You can also download a project breakdown report in the "Usage History" tab of Settings > Subscriptions (only accessible to Owner and Billing members of your Sentry organization).
Sentry's flexibility means you can exercise fine-grained control over which events and attachments count toward your quota. This page provides you with high-level information about strategies for managing your quota, but you can get more detailed information in:
- Spike Protection
- Manage Your Error Quota
- Manage Your Span Quota
- Manage Your Replay Quota
- Manage Your Attachments Quota
There are a number of things you can do to manage your quota, as shown in the table below. Actions are listed in order from easiest and fastest, to most challenging and potentially time-consuming. The checkmarks tell you whether the action helps you manage errors, spans, replays, attachments, or some combination of the four.
The first 6 actions in the list can all be done in sentry.io, while the rest have to be done in an SDK.
| Action | Errors | Spans | Replays | Attachments |
|---|---|---|---|---|
| Ensure spike protection is enabled | ✓ | ✓ | ✓ | |
| Adjust your quota | ✓ | ✓ | ✓ | ✓ |
| Rate limit your events or attachments | ✓ | ✓ | ||
| Review repeated events | ✓ | |||
| Filter your events | ✓ | ✓ | ✓ | |
| Update your SDK sample rate | ✓ | ✓ | ||
| Apply SDK filtering | ✓ | ✓ | ||
| Update your SDK configuration | ✓ | ✓ | ||
| Manage data size | ✓ | ✓ | ✓ |
Sentry completes a thorough evaluation of each event to determine if it counts toward your quota, as outlined in this overview. Detailed documentation for each evaluation is linked throughout.
Before completing any of these evaluations, Sentry confirms that each event includes a valid DSN and project as well as whether the event can be parsed. In addition, for error events, Sentry validates that the event contains valid fingerprint information. If any of these items are missing or incorrect, the event is rejected.
This list is ordered from easiest or least time-consuming, to most challenging or potentially time-consuming.
Spike Protection protects users from spiking event volume. Typically, spikes are caused by anomalies and have the potential to deplete your available event volume rapidly. Your baseline consumption is used to compute a threshold and spike protection is triggered if event volume exceeds this threshold. When spike protection is triggered, events start getting dropped, ensuring that you don't get charged for the excess volume.
Spike Protection can be enabled on a per-project basis for your organization by any team member with either Billing or Owner-level permissions. To select which project to set it up for, go to Settings > Spike Protection. You'll be able to toggle it on for individual projects or click “Enable All” to set it up for all your projects at once. Learn more about how spike protection works and how to manage spikes in Spike Protection.
Events and attachments that exceed your quota will not be accepted, so you may want to increase your quota. Conversely, you might want to decrease your quota or adjust your reserved and pay-as-you-go quotas to better control your spending. Learn about adjusting your quota in Manage Your Error Quota, Manage Your Span Quota, Manage your Replay Quota, and Manage Your Attachments Quota.
You can add limits for error events on a per-project basis in [Project] > Settings > SDK Setup > Client Keys (DSN). If the event rate limit for a project has been exceeded, and your subscription allows, the event won't be counted. You can also rate limit attachments on an organization level in Settings > Security & Privacy. Learn more in Manage Your Error Quota and Manage Your Attachments Quota.
In some cases, repeated events can count against your quota, so it's important to know how event repetition is treated in Sentry. Learn more in Manage Your Error Quota.
If an inbound filter is applied for a type of error, transaction/span, or attachment, and your subscription allows, it won't be counted. You can manage these in [Project] > Settings > Inbound Filters. Learn more in Manage Your Error Quota, Manage Your Span Quota, Manage your Replay Quota, and Manage Your Attachments Quota.
If a sample rate is defined for the SDK, the SDK evaluates whether this event should be sent as a representative fraction of events, effectively limiting the number of errors and transactions/spans you send to Sentry. Setting a sample rate is documented for each SDK, but you can also learn more in Manage Your Error Quota and Manage Your Span Quota.
All Sentry SDKs support the beforeSend callback method, which you can use to modify the data of an error event or to drop it completely. Many also support beforeSendTransaction. Learn more in Manage Your Error Quota and Manage Your Span Quota.
The SDK configuration either allows an event to be sent to Sentry or filters it out. Configuration is documented for each SDK, but you can also learn more in Manage Your Error Quota and Manage Your Span Quota.
Sentry imposes limits on various fields within an event, as well as the size of full events and the requests they are sent in, which can affect your attachments quota. Learn more in Manage Your Attachments Quota.
Use this table as a quick reference for what does and doesn't count towards your quota:
| Scenario | Yes, this data counts |
|---|---|
| Spike protection activation threshold has been reached (errors) | |
| Spike protection no longer active (errors) | ✓ |
| Your quota hasn't been reached | ✓ |
| Your quota has been exceeded | |
| A rate limit for a project has been applied (errors, attachments) | |
| This is a repeated event for which issues were previously set to Delete & Discard (errors) | |
| This is a repeated event for a previously resolved issue (errors) | ✓ |
| This is a repeated event for an issue that you've set to Ignore | ✓ |
| The event defies inbound filters configured in sentry.io | |
| The event is sent after the SDK sample rate has been exceeded | |
| The event isn't sent based on SDK filters | |
| The event isn't sent based on SDK configuration | |
| Size limits have been exceeded |
Sentry groups accepted errors and spans into issues. The issues themselves don't count towards your quota, but the errors and spans that comprise an issue are counted.
Let's clarify a few terms:
- Attachment - Attachments are stored additional files, such as config files, log files, or stored mini-dumps, that are related to an error event. Unless the option to store crash reports is enabled, Sentry will use these files only to create an event, and then drop them.
- Cron Monitor - A Cron Monitor represents a set of configurations for a scheduled, recurring job such as a "Data Backup" job that runs daily on production and development.
- Data - Anything you send to Sentry. This includes events (errors, spans, or replays), attachments, and event metadata.
- Error - What counts as an error varies by platform, but in general, if there's something that looks like an exception, it can be captured as an error in Sentry. Sentry automatically captures errors, uncaught exceptions, and unhandled rejections, as well as other types of errors, depending on platform. A grouping of similar errors makes an issue.
- Event - An event is one instance of you sending data to Sentry, excluding attachments. Generally, this data is an error or a transaction/span.
- Replay - Session Replays are video-like reproductions of users' sessions as they navigate your app or website.
- Span - A billing unit in Sentry that maps to span usage. Also the basic unit that traces are composed of. Multiple spans make up a trace in Sentry and share a trace_id.
- Profile - A snapshot of your code's resource usage obtained by periodically capturing the call stack as your application runs.
- Quota - Your quota is the amount of data (errors, spans, replays, attachments) that you pay Sentry to track.
Our documentation is open source and available on GitHub. Your contributions are welcome, whether fixing a typo (drat!) or suggesting an update ("yeah, this would be better").