Bitbucket
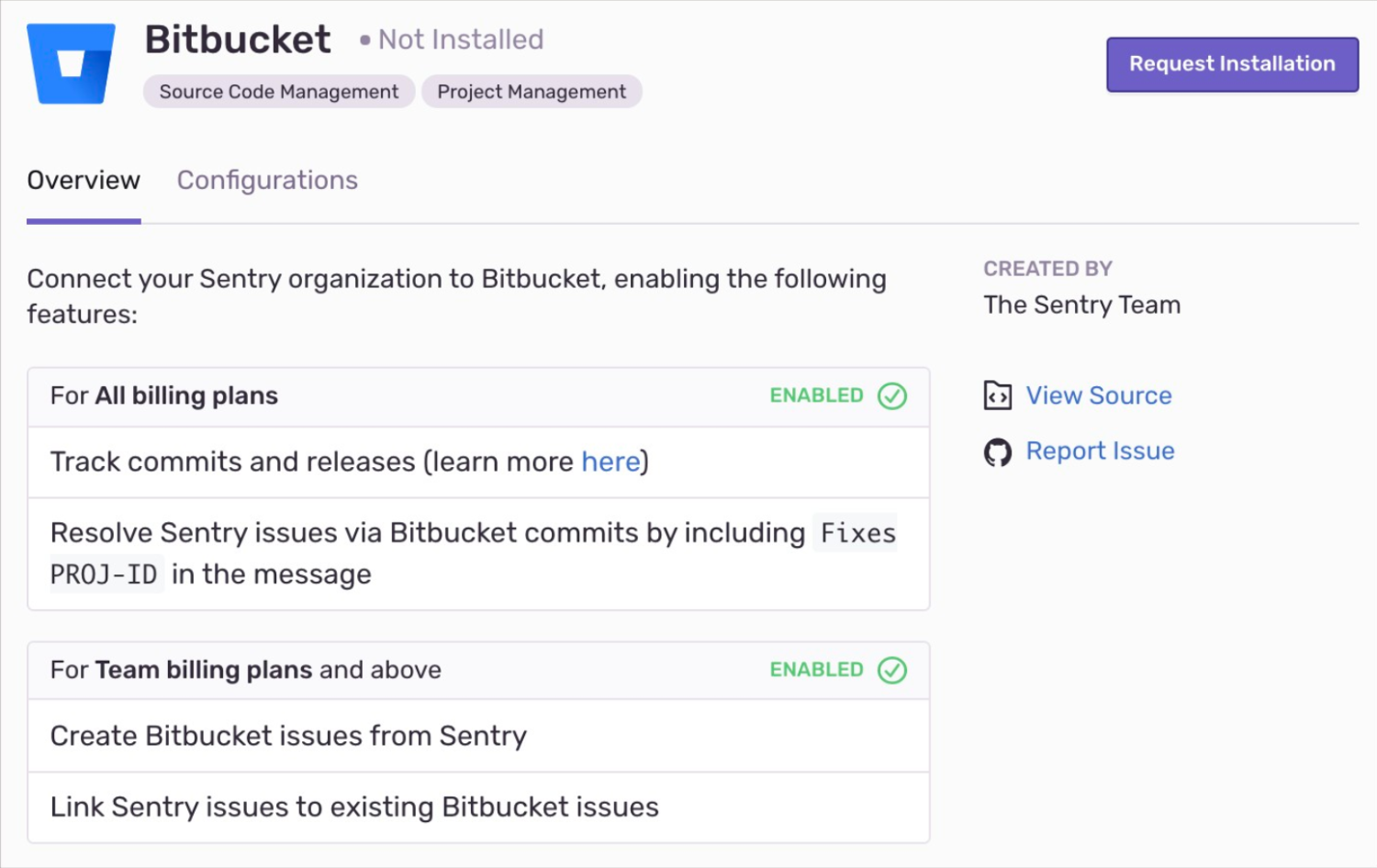
Learn more about Sentry's Bitbucket integration and how it can track and resolve bugs faster by using data from your Bitbucket commits.
Sentry owner, manager, or admin permissions, and Bitbucket admin permissions are required to install this integration.
- Navigate to Settings > Integrations > Bitbucket.
If you have the legacy Bitbucket integration installed, use the button next to Bitbucket to Upgrade. If you don't have the legacy Bitbucket integration installed, use the button to Install.
In the resulting modal, click "Add Installation".
A Bitbucket install window should pop up. Select the Bitbucket account you'd like to grant Sentry access to, and click "Grant Access".
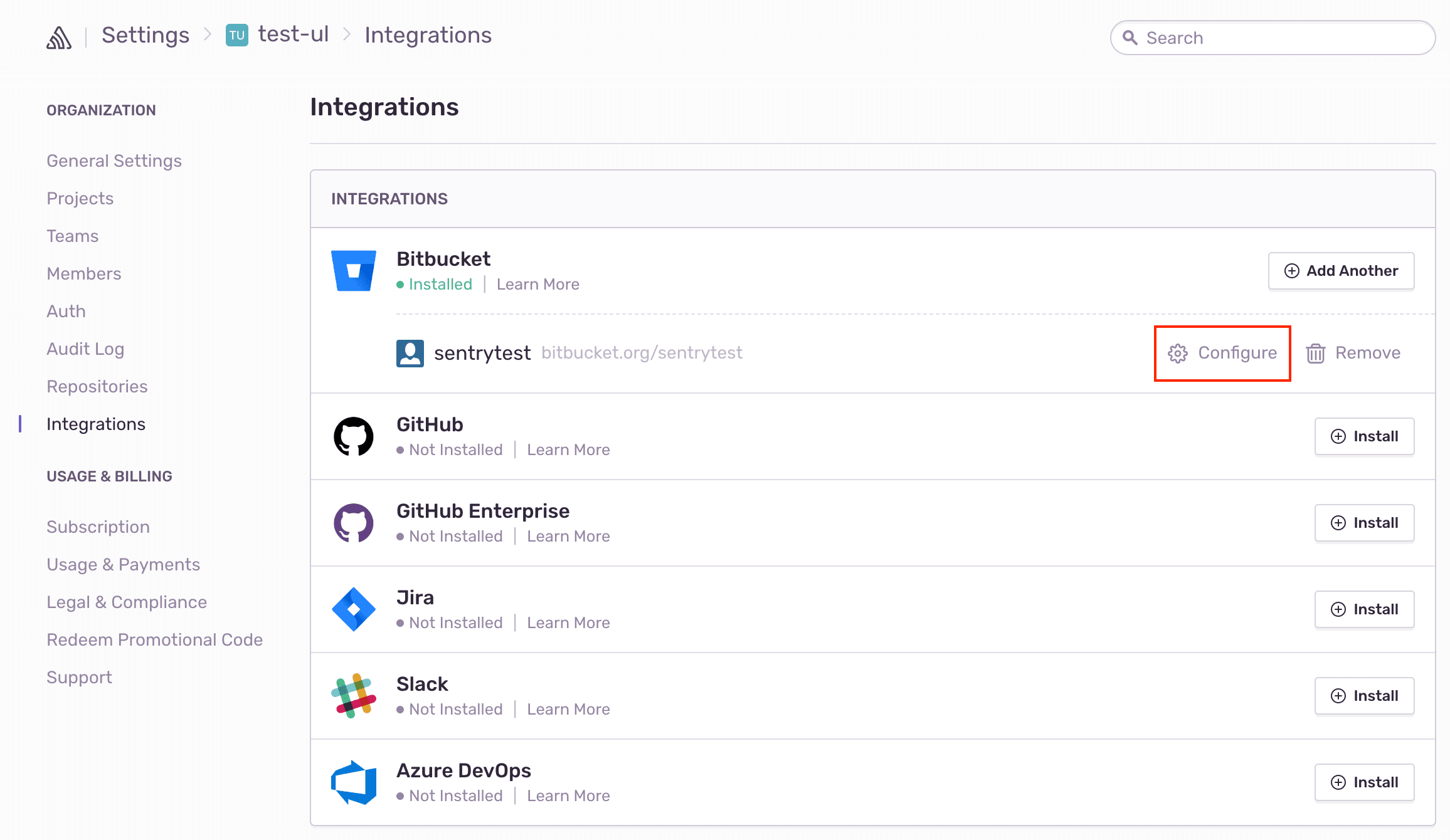
On your new Bitbucket instance in Sentry, click "Configure".
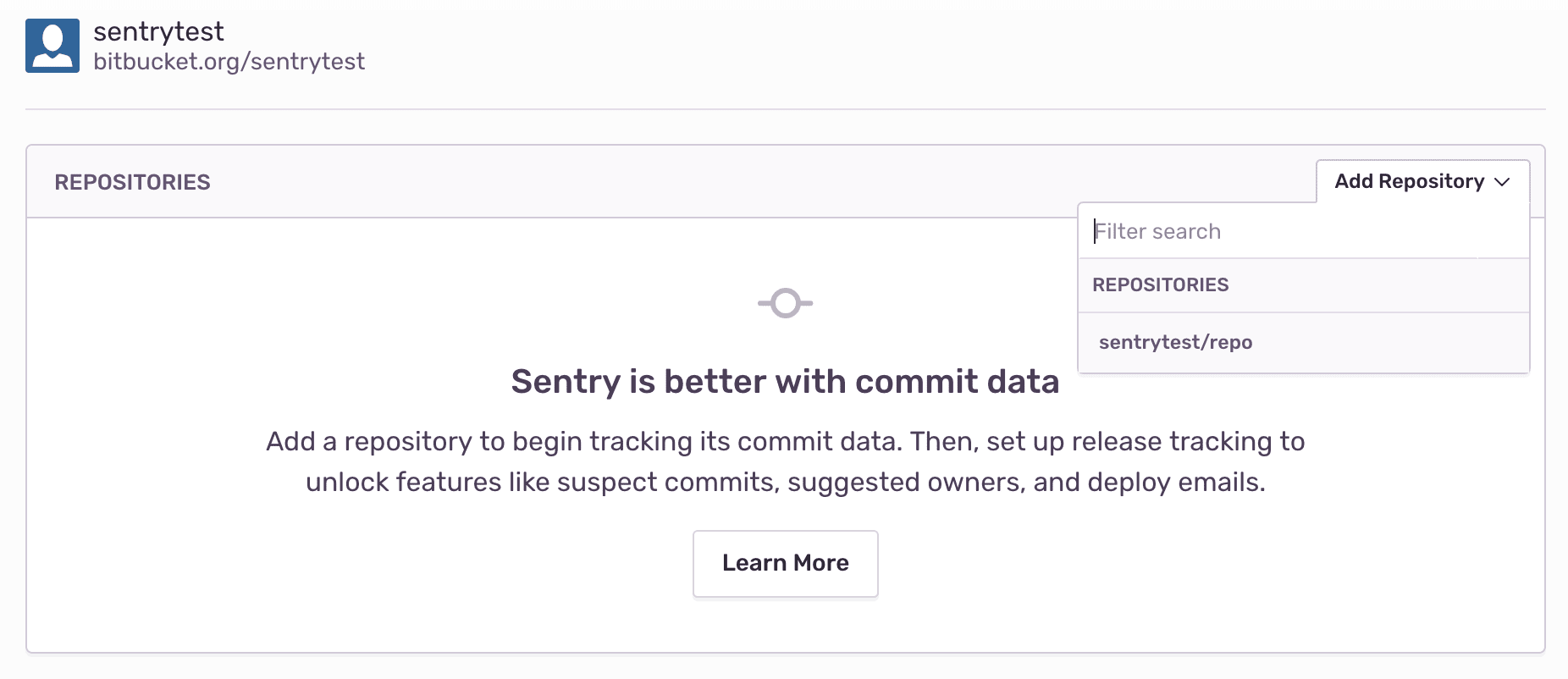
Add any repositories from which you want to collect commit data.
Bitbucket should now be enabled for all projects under your Sentry organization.
To generate an RSA public/private key pair, run the following commands in your terminal window one by one.
openssl genrsa -out bitbucket_privatekey.pem 1024
openssl req -newkey rsa:1024 -x509 -key bitbucket_privatekey.pem -out bitbucket_publickey.cer -days 365
openssl pkcs8 -topk8 -nocrypt -in bitbucket_privatekey.pem -out bitbucket_privatekey.pcks8
openssl x509 -pubkey -noout -in bitbucket_publickey.cer > bitbucket_publickey.pem
In Bitbucket, click the gear icon, then Applications > Application Links.
For "Application Type", make sure "Atlassian Product" is selected.
Enter the following as the application URL:
https://sentry.io/extensions/bitbucket_server/setup/Click "Create New Link". If you see a warning that “No response was received from the URL you entered,” ignore and click "Continue".
In the Configure Application URL modal, your URL from the last screen should show up in the "Entered URL" box, make sure to check "Use this URL" before hitting "Continue".
In the resulting dialog, fill out the form as follows:
Application Name Sentry Application Type Generic Application Service Provider Name Sentry Consumer Key (your choice, but keep this handy for the next step) Shared Secret sentry Request Token URL https://sentry.io Access Token URL https://sentry.io Authorize URL https://sentry.io Create Incoming Link No Click "Continue". This will return you to the Configure Application Links page, where you'll see an application called Sentry.
Click the pencil icon next to the Sentry application.
On the left hand side of the resulting modal, click "Incoming Authentication". Fill out the form as follows, and click "Save":
Consumer Key (the consumer key from Step II.4) Consumer Name Sentry Public Key (the public key you created in Section I) Consumer Callback URL https://sentry.io/extensions/bitbucket_server/setup/ Allow 2-Legged OAuth no
Note: Confirm Sentry's IP ranges are allowed.
- In Sentry, navigate to Organization Settings > Integrations.
- Next to Bitbucket Server, click "Install".
- In the resulting modal, click "Add Installation".
- In the resulting window, enter the base URL for your Bitbucket Server instance, your consumer key, and your private key. Click "Submit". Then, complete the OAuth process as prompted.
- In Sentry, you’ll see a new Bitbucket Server instance appear on the Integrations page.
Bitbucket should now be authorized for all projects under your Sentry organization.
Use Bitbucket to track commits, for issue management, and to resolve in commit.
Commit tracking allows you to hone in on problematic commits. Uncover which commits likely caused an issue, and allow your team to resolve issues by referencing the issue number in a commit message.
For more details, see the full documentation on commit tracking and releases.
This feature is only supported on legacy Bitbucket instances. See Bitbucket Support for more details.
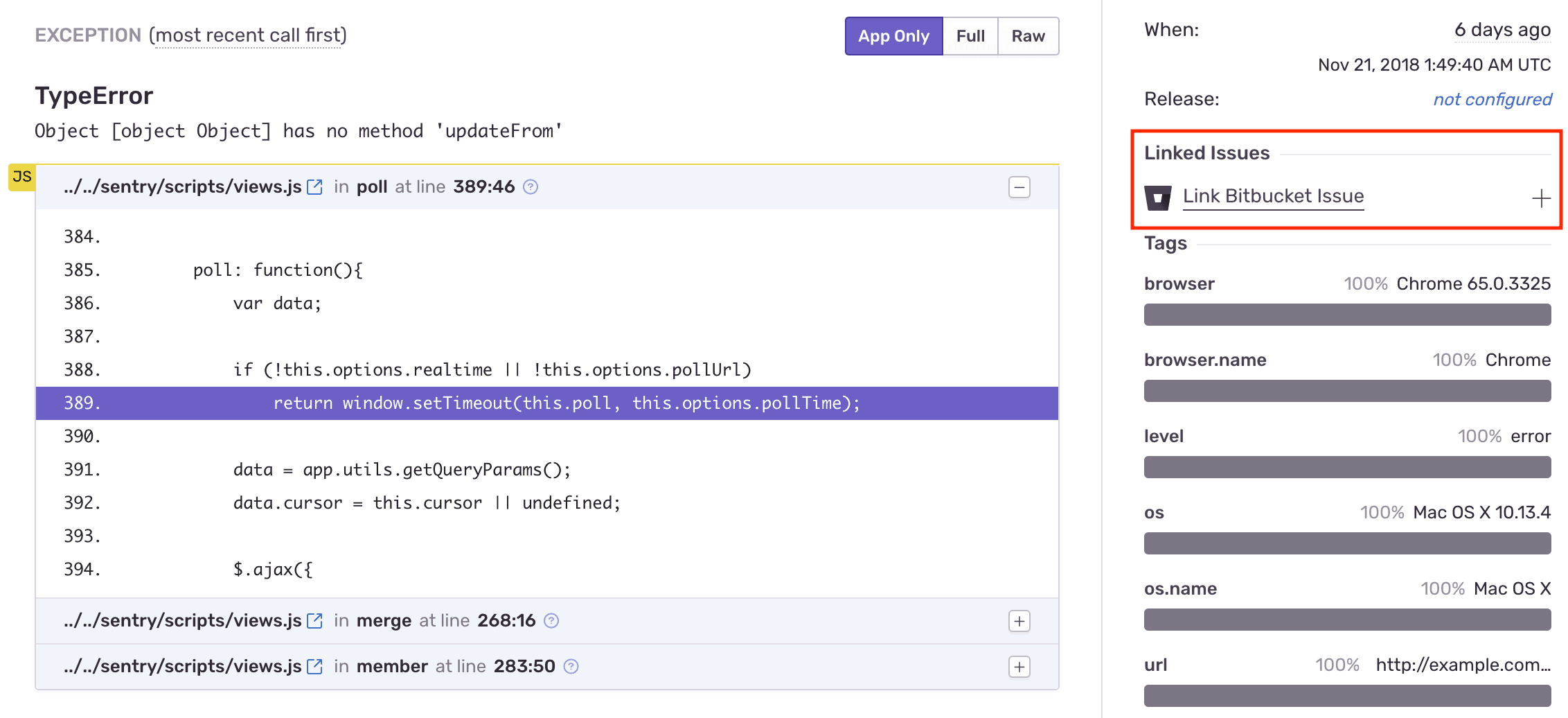
Issue tracking allows you to create Bitbucket issues from within Sentry, and link Sentry issues to existing Bitbucket Issues.
Once you’ve navigated to a specific issue, you’ll find the Linked Issues section on the right hand panel. Here, you’ll be able to create or link Bitbucket issues.
Once you are sending commit data, you can start resolving issues by including fixes <SENTRY-SHORT-ID> in your commit messages. For example, a commit message might look like:
Prevent empty queries on users
Fixes MYAPP-317
When Sentry sees this, we’ll automatically annotate the matching issue with reference to the commit, and later, when that commit is part of a release, we’ll mark the issue as resolved. The commit must be associated with a release. Otherwise, if the commit is squashed, Sentry won’t know when the commit has been released, and the issue may never be marked as a regression.
Stack trace linking takes you from a file in your Sentry stack trace to that same file in your source code. If you have commit tracking set up in Sentry, we can take you to the exact version (using the commit associated with the event) of the source code when the error occurred. Otherwise we'll link you to the current state of the source code (using the default branch).
Navigate to Settings > Integrations > Bitbucket > Configurations.
Click "Configure" (the gear icon) next to your Bitbucket Instance.
Click the "Code Mappings" tab.
Set up a code mapping for each project you want to have stack trace linking. To create a new code mapping, click "Add Mapping".
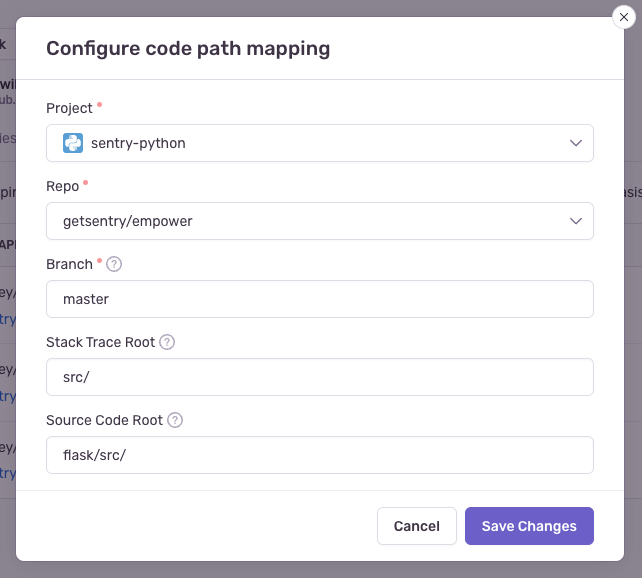
Fill out the form, then click "Save Changes". Each form field is described below:
- Project (required): This is the Sentry project.
- Repo (required): This is the Bitbucket project associated with the Sentry project above. If you have more than one Bitbucket project being used per Sentry project, you'll need multiple code mappings.
- Branch (required): This is the default branch of your code we fall back to if you do not have commit tracking set up.
- Stack Trace Root and Source Code Root (optional): See below for information on determining these values.
The following information is only valid for platforms which use traditional file paths. Platforms with package names require additional steps. For Java, read more in the page on source context.
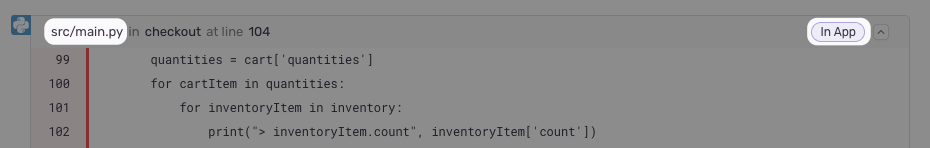
First, navigate to a stack trace that you wish to map. Find an In App frame, which is denoted by a bubble on the right side of the frame. The filename will be shown as the first piece of text at the left hand side of the frame header. In this example, it is src/main.py.
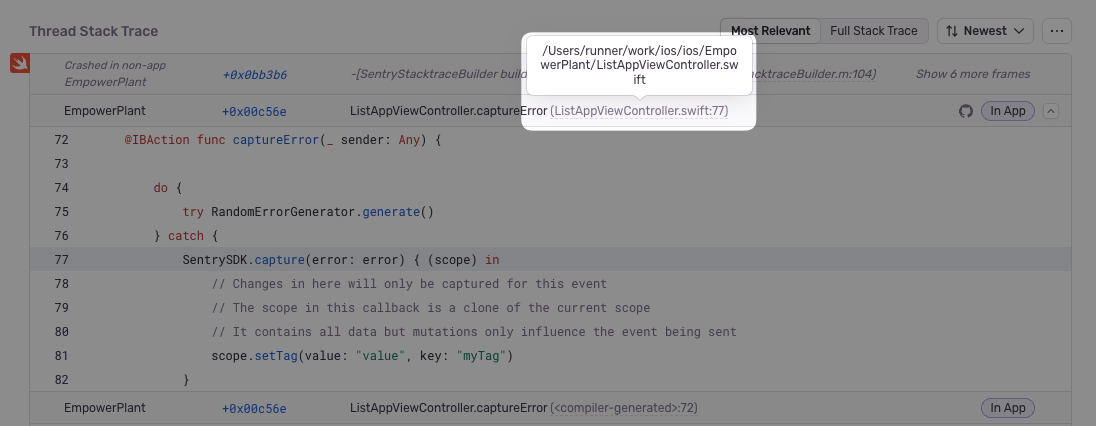
For certain native platforms, the stack trace will look different. In cases like these, you can find the absolute path by hovering over the filename.
If you aren’t sure, you can look at the event JSON by clicking on the {} button in the event header. Find the text in the frame's filename or abs_path.
Next, locate the file seen in the stack trace with your source code provider (e.g. GitHub). In this example, the path is flask/src/main.py (empower is ignored since it is the name of the repo).
Compare the file path from the stack trace with the path found in your source repository. In this example, the src/ folder in the stack trace matches the flask/src folder in the source code. Using that information, set the Stack Trace Root to src/ and the Source Code Root to flask/src/. This tells Sentry to replace all file paths beginning in src/ with flask/src/ when searching for the source code.
For best results, we recommend always providing a non-empty value for the Stack Trace Root when possible.
If you're having trouble setting up Sentry with your on-premises integration, verify the following:
- The provided installation URL is a fully qualified domain name (FQDN), which is resolvable on the internet.
- The IP addresses Sentry uses to make outbound requests are allowed.
- Sentry's access to your installation URL is not path restricted.
Our documentation is open source and available on GitHub. Your contributions are welcome, whether fixing a typo (drat!) or suggesting an update ("yeah, this would be better").